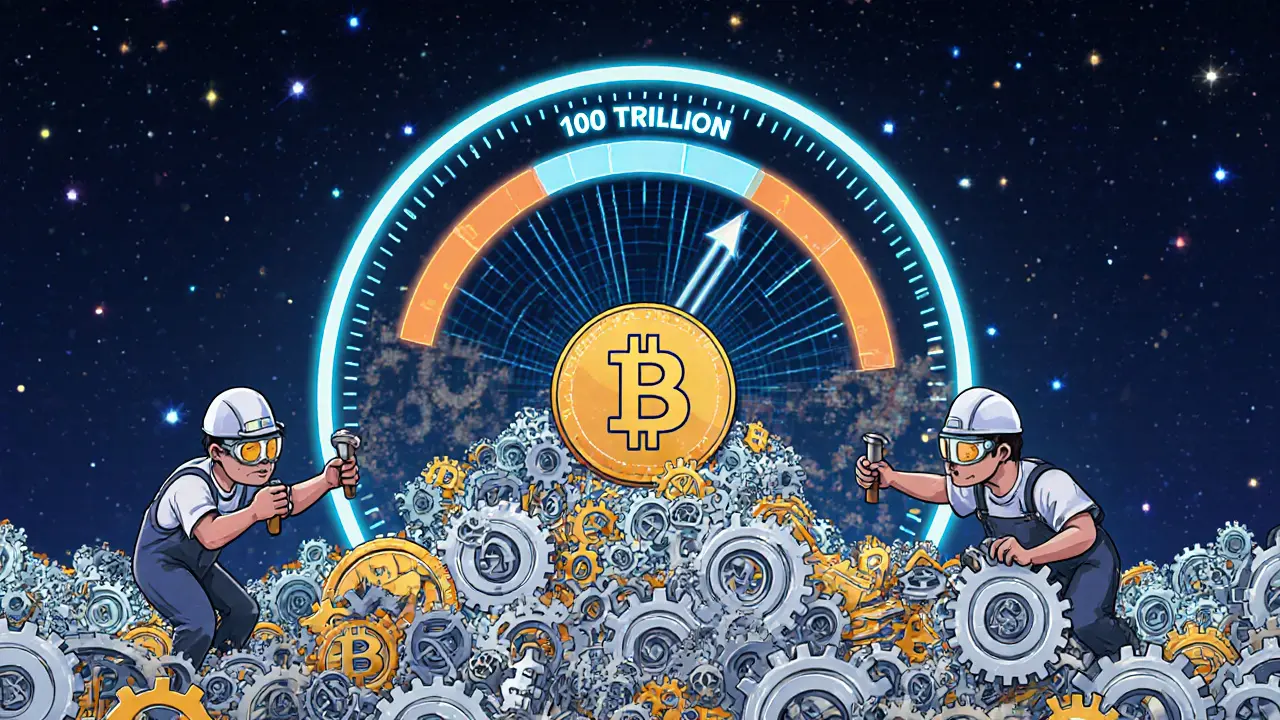
How 51% Attacks Work in Proof of Work Blockchains
A 51% attack lets a single entity control more than half of a blockchain's mining power to reverse transactions and double-spend coins. Small cryptocurrencies are vulnerable - Bitcoin isn't. Here's how it works and how to stay safe.
Read More