Imagine you’re at a town hall meeting. One person stands up and speaks for themselves. Then, suddenly, fifty people stand up, all wearing identical masks, all repeating the same speech, all voting for the same candidate. The majority isn’t real-it’s an illusion created by one entity pretending to be many. This is exactly what happens during a Sybil attack on a blockchain network.
In the world of distributed ledgers, trust is built on the assumption that each node represents a unique participant. But when malicious actors create hundreds or thousands of fake nodes-known as Sybil nodes-they can manipulate consensus, drain liquidity from DeFi protocols, or even hijace governance votes. Detecting these hidden identities is one of the most critical challenges in modern blockchain security.
What Is a Sybil Attack?
The term “Sybil” comes from a 2002 research paper titled The Sybil Attack, written by Brian Neil Levine and Clay Shields from the University of Massachusetts Amherst. They used the name to describe a scenario where a single adversary controls multiple pseudonymous identities to gain disproportionate influence over a peer-to-peer network.
In blockchain terms, a Sybil attack occurs when an attacker creates numerous fake nodes to:
- Control more than 51% of the network’s hashing power (in Proof-of-Work systems)
- Manipulate validator sets (in Proof-of-Stake systems)
- Fraudulently claim airdrops or governance rights
- Disrupt network communication or censor transactions
A famous example happened in January 2019, when the Ethereum Classic network suffered a successful Sybil-assisted 51% attack. Attackers controlled enough nodes to reverse transactions and double-spend coins, causing millions in losses. It was a stark reminder that decentralization doesn’t automatically mean security.
Why Sybil Detection Matters
Without effective detection mechanisms, blockchains are vulnerable to centralization under false pretenses. A network might appear highly decentralized-with thousands of nodes spread across dozens of countries-but if 60% of those nodes are controlled by one entity, it’s no different from a centralized server.
The consequences go beyond technical failures. In 2022 alone, Formo reported 37 documented Sybil attacks targeting DeFi protocols, with average losses of $2.8 million per incident. Many of these targeted airdrop distributions, where bots claimed tokens meant for genuine users. Optimism’s retroactive airdrop, for instance, initially estimated that 68% of claims were fraudulent. After implementing 14 Sybil detection filters, that number dropped to just 8.3%, saving approximately $142 million in token value.
Regulators are taking notice too. The EU’s MiCA regulations, effective June 2024, require robust Sybil attack prevention for all blockchain networks operating within Europe. Meanwhile, the SEC’s proposed Digital Asset Security Framework mandates industry-standard Sybil detection mechanisms by 2026. These aren’t optional features anymore-they’re legal requirements.
How Do We Detect Sybil Nodes?
There’s no silver bullet. Instead, developers rely on layered approaches combining economic, behavioral, and cryptographic signals. Here are the five main methods currently in use:
1. Social Trust Graph Analysis
This method maps connections between nodes to identify clusters of suspicious behavior. If ten nodes always vote together, share IP ranges, or interact in unnatural patterns, they’re likely part of the same Sybil cluster. Research from the IEEE Symposium on Security and Privacy (2021) shows this approach achieves 86.3% accuracy in identifying such groups.
2. Identity Verification Layers
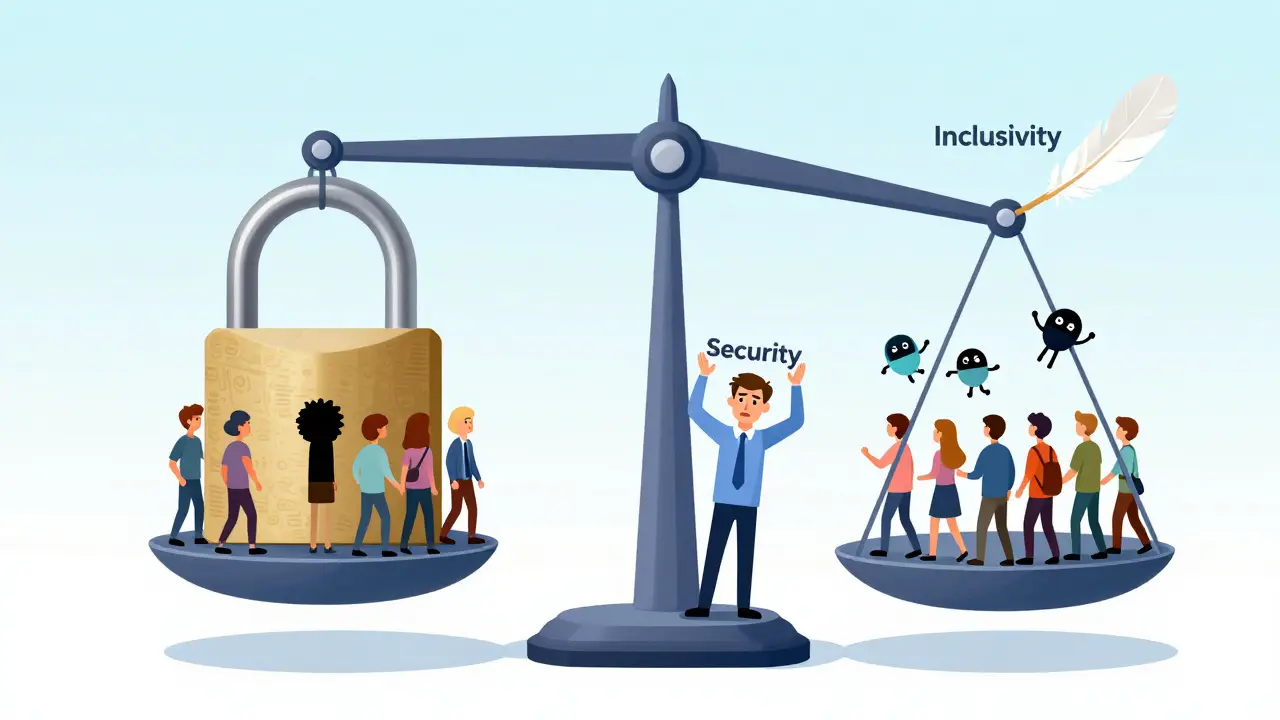
Some platforms require phone numbers, credit cards, or biometric scans to prove human identity. Coinbase found that phone verification reduced Sybil wallet creation by 74%, while credit card checks lowered it by 89%. However, World Bank data reveals these methods exclude 28% of potential users in developing markets-a significant trade-off between security and accessibility.
3. Reputation Systems
Chainlink’s oracle network uses reputation scoring based on consistent positive behavior over time. New nodes start with low trust levels and must operate reliably for 90-180 days before reaching maximum credibility. This makes short-term Sybil attacks economically unfeasible since attackers can’t build up sufficient reputation quickly.
4. Economic Barriers
Proof-of-Work and Proof-of-Stake inherently deter Sybil attacks through cost. Bitcoin requires controlling 51% of hashrate-an effort costing around $1.4 million per hour as of July 2023. Ethereum’s Proof-of-Stake demands validators stake 32 ETH (~$89,600 at October 2023 prices). While not perfect, these costs make large-scale Sybil operations prohibitively expensive.
5. Biometric & Personhood Protocols
Worldcoin’s Orb device attempts to verify one-person-one-identity using iris scanning. By August 2023, it had verified 2.3 million unique users. Though promising, such systems face adoption hurdles in fully permissionless networks due to privacy concerns and hardware dependency.
| Method | Accuracy | Privacy Impact | Implementation Cost | False Positive Rate |
|---|---|---|---|---|
| Social Trust Graph | 86.3% | Low | Medium | ~18.7% |
| Identity Verification | Up to 89% | High | High | Low |
| Reputation Systems | Varies | Medium | Medium | 4.3% (with adaptive models) |
| Economic Barriers | N/A (deterrence-based) | None | Very High | N/A |
| Biometric Protocols | 99.2% (zkSync testnet) | Very High | Very High | Minimal |

Challenges in Implementation
Detecting Sybil nodes isn’t just about technology-it’s about balancing competing priorities. Developers report several persistent issues:
- High False Positives: Legitimate users often get flagged. On Reddit, developer u/EthereumSecurityExpert noted their DAO saw false positives drop from 22% to 4.3% after tuning thresholds-but only after increasing infrastructure costs by 37%.
- Computational Overhead: Advanced detection adds 8-12% latency to transaction processing according to Consensys’ 2023 report. For high-throughput chains, this matters.
- Accessibility Trade-offs: MIT’s Digital Currency Initiative warns that identity verification excludes 1.7 billion unbanked adults globally. Security shouldn’t come at the expense of inclusion.
- Privacy Concerns: A Blockchain Council survey found 74.2% of developers cite maintaining user privacy as the top challenge in Sybil detection.
Open-source tools like SybilRank (867 GitHub stars as of October 2023) help mitigate some costs, but reviews highlight complaints about “high computational overhead for small networks.” Enterprise teams fare better: JPMorgan’s Quorum network reported zero Sybil incidents after multi-factor ID verification, though onboarding times increased by 23%.
Emerging Technologies Shaping the Future
New innovations aim to solve old problems without sacrificing usability or privacy:
Zero-Knowledge Proofs (ZKPs)
zkSync demonstrated 99.2% accuracy in detecting Sybil wallets while preserving user privacy during its October 2023 testnet deployment. ZKPs allow users to prove they’re human without revealing personal details-a major step forward for decentralized identity.
AI-Driven Behavioral Analysis
The World Economic Forum highlights AI-driven analysis combined with decentralized identity protocols as the next frontier. Early tests show 96.8% accuracy in identifying Sybil clusters while maintaining 98.3% compliance with privacy standards.
Decentralized Identity Standards
Projects like DIDComm and W3C Verifiable Credentials are laying groundwork for portable, interoperable identity systems. Unlike closed-loop verifications, these let users control their own credentials while enabling cross-platform Sybil resistance.
Upcoming Protocol Upgrades
Ethereum’s Pectra upgrade (Q1 2025) includes EIP-7251, which enhances validator identity verification via improved stake concentration analysis. Bitcoin’s BIP-325 proposal explores “Proof of Personhood,” gaining 87% support among developers in September 2023 surveys.
Real-World Lessons from Recent Attacks
Learning from past mistakes helps shape future defenses. Consider Monero’s 2021 Sybil incident: attackers controlled 42% of network nodes, exploiting anonymity features designed to protect legitimate users. The lesson? Privacy-focused designs need additional safeguards against coordinated manipulation.
Similarly, EOS’s Delegated Proof-of-Stake model limits block producers to 21 entities, reducing Sybil risk but also lowering decentralization scores (5.8/10 vs Bitcoin’s 9.2/10 per CryptoRank). There’s always a trade-off between efficiency and openness.
Optimism’s experience offers another valuable case study. Their initial airdrop filter missed many sophisticated bots. Only after deploying machine learning models trained on historical interaction patterns did they achieve meaningful reduction in fraud. Community backlash followed-user u/OptimismUser123 spent 17 days resolving a false flag. Clear appeal processes matter as much as accurate detection.
Building Resilient Networks: Best Practices
If you’re designing or securing a blockchain system, here’s what experienced engineers recommend:
- Start Simple: Begin with basic threshold configurations (e.g., minimum stake requirements) before layering complex algorithms.
- Monitor Behavior, Not Just Identity: Track how nodes behave over time-not just who they claim to be.
- Use Adaptive Thresholds: Static rules fail against evolving tactics. Chainlink’s progressive trust scoring reduces false positives dynamically.
- Plan for Appeals: Build transparent dispute resolution into your protocol. Users deserve recourse when wrongly flagged.
- Test Under Stress: Simulate Sybil scenarios regularly. Red team exercises reveal blind spots before attackers do.
Expect a learning curve: Consensys Academy estimates 3-5 weeks for basic implementation, 8-12 for advanced setups. Key skills include network security expertise (cited by 87% of devs), cryptography knowledge (76%), and behavioral analysis capabilities (63%).
Looking Ahead: What Comes Next?
By 2027, Gartner predicts networks lacking robust Sybil detection will suffer 73% higher failure rates. Conversely, those adopting multi-layered strategies could cut operational security costs by 41%. The global blockchain security market-including Sybil solutions-is projected to hit $18.7 billion by 2027, growing at 52.3% annually.
Enterprise adoption is accelerating: 63% of Fortune 500 companies now implement some form of Sybil protection, per Gartner’s October 2023 survey. Startups like Formo ($22M Series A raised in August 2023) focus specifically on Sybil-resistant user acquisition, signaling strong commercial interest.
But progress brings tension. DappRadar’s 2023 analysis shows networks with advanced detection see 32.7% fewer bot accounts-but also 14.3% lower overall user growth. Balancing security with inclusivity remains the core dilemma.
As Vitalik Buterin noted in his January 2023 blog post, “Proof-of-stake fundamentally changes the Sybil attack landscape by making identity acquisition expensive rather than merely difficult.” That shift-from difficulty to cost-is reshaping how we think about trust in decentralized systems.
What is a Sybil node?
A Sybil node is a fake identity created by a single attacker to mimic multiple independent participants in a blockchain network. These nodes work together to distort consensus, manipulate voting, or exploit incentives like airdrops.
Can Sybil attacks happen on any blockchain?
Yes, especially those relying purely on node count for decentralization metrics. Even Proof-of-Stake networks aren’t immune if staking thresholds are too low or identity verification is weak. However, economic barriers significantly raise the cost of executing such attacks.
How accurate are current Sybil detection methods?
Accuracy varies widely. Social graph analysis reaches ~86.3%, biometric systems hit 99.2% in controlled environments, and AI-enhanced models achieve up to 96.8% accuracy while preserving privacy. No method is flawless, hence the need for layered defenses.
Do Sybil detection systems hurt regular users?
Sometimes. False positives occur frequently-averaging 18.7% across networks unless mitigated. Some users face delays or rejection despite legitimate activity. Good systems balance precision with fair appeal mechanisms to minimize harm.
Will regulation force all blockchains to adopt Sybil detection?
Increasingly yes. The EU’s MiCA framework already requires it for European operations. The U.S. SEC proposes mandatory industry-standard mechanisms by 2026. Compliance will become non-negotiable for public-facing blockchain services.
Is there a perfect solution to Sybil attacks?
No. As Dr. Ari Juels states, “No purely technical solution can completely eliminate Sybil attacks.” The best defense combines economic disincentives, behavioral monitoring, and social verification layers-all tailored to specific network goals.
How long does it take to implement Sybil detection?
Basic implementations take 3-5 weeks; advanced ones require 8-12. Phases include network behavior analysis (2-3 weeks), threshold configuration (1-2 weeks), and integration testing (2-4 weeks). Teams should budget accordingly and plan for iterative refinement.
What’s the biggest challenge in building Sybil-resistant systems?
Balancing security with accessibility. Strict verification excludes billions of unbanked users. Loose detection invites abuse. Finding the right middle ground-without compromising either goal-is the ongoing struggle facing every blockchain project today.
